Claude Code Routines: The Architecture That Replaced My Entire Cron Infrastructure
Quick Answer
Claude Routines are cloud-native scheduled AI agents that run full Claude Code sessions on Anthropic's infrastructure. Three trigger types (schedule, API, GitHub events), MCP connectors for typed tool access, and branch protection by default. Production-ready with caveats: no idempotency key, shared rate limits, and research-preview API instability.
I had the usual setup. Cron jobs triggering shell scripts that called APIs, parsed output, wrote to databases, and sent Slack notifications. Four services, three failure modes, zero self-healing.
Then I replaced it with five Claude Routines in an afternoon.
Here's the architecture that survived, and the parts that almost broke.
The Execution Model
Definition
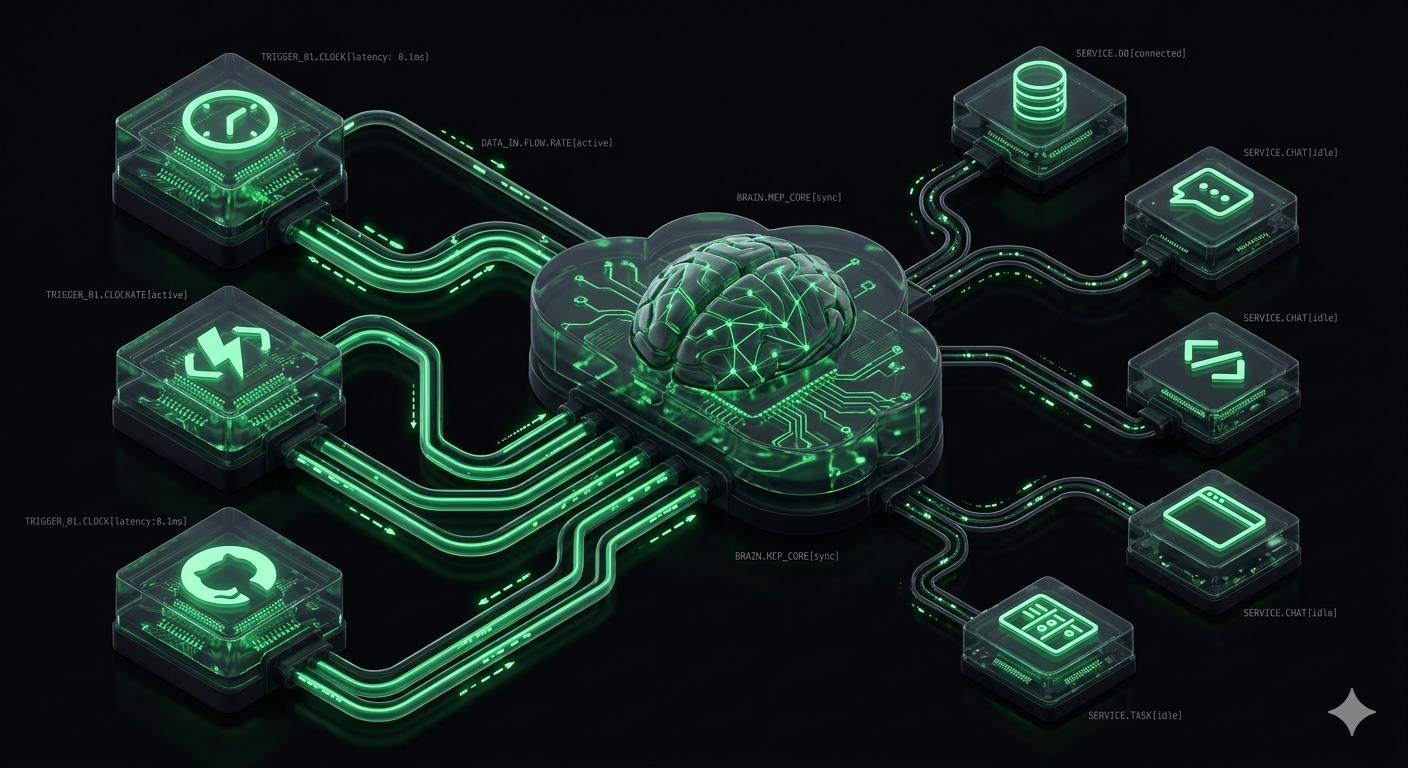
A saved Claude Code configuration — prompt, repository, and connectors — that runs as a full reasoning session on Anthropic's cloud infrastructure. Each run gets the same capabilities as an interactive Claude Code session: tool use, MCP access, multi-file editing, and error recovery.
The key insight is that each routine run isn't a simple script execution. It's a complete Claude Code session. The agent reads your codebase, reasons about the task, calls tools, handles errors, and adapts its approach when something fails.
This is fundamentally different from n8n or Make, where you define deterministic node-by-node execution. A routine handles the branching logic implicitly through reasoning.
Trigger Architecture
Three trigger types, combinable on a single routine:
Scheduled Triggers
Standard cron-style scheduling: hourly, daily, weekdays, weekly, or one-shot at a specific future time. Set via the web UI at claude.ai/code/routines or CLI with /schedule.
API Triggers (/fire Endpoint)
POST https://api.anthropic.com/v1/claude_code/routines/{routine_id}/fire
Required header:
anthropic-beta: experimental-cc-routine-2026-04-01
Bearer token generated per-routine — shown once on creation, cannot be retrieved later. Store it securely.
Critical production gotcha: No idempotency key. Each POST creates a new session. If your webhook caller retries on timeout, you get duplicate runs. Build a dedup layer or use Retry-After header parsing on 429s.
GitHub Triggers
Runs on repository events: pull_request.opened, release.published, etc. Filter by event type, branch, or label. This is the native event-driven trigger — no third-party webhook plumbing needed for GitHub-centric workflows.
MCP Connectors: The Tool Layer
Routines interact with external systems through Model Context Protocol connectors. These aren't free-form API calls — they're typed tool contracts:
- GitHub: Repository access, issue management, PR operations
- Slack: Channel messaging, thread replies
- PostgreSQL: Direct database queries
- Browsers: Web scraping and interaction via automation tools
- Jira/Asana: Project management read/write
The governance model: test in sandbox first, enforce read-only tools initially, add human-in-the-loop gates before granting write permissions. Production logging should capture: trigger event, tools called, target resources, acting user, resulting object IDs.
Branch Protection
By default, routines push only to branches prefixed claude/. This prevents a misconfigured routine from writing directly to main. Disable only when you have robust downstream review processes (required PR approvals, CI gates).
5 Production Patterns That Survived Real Workloads
I've been running these for three weeks. Here's what actually works:
Pattern 1: Nightly Issue Triage
The routine reads all issues opened in the last 24 hours, cross-references the codebase to identify affected modules, assigns priority based on component criticality, and posts a structured triage summary to Slack.
Unlike a script-based triage that matches keywords, the routine actually reads the code referenced in the issue and makes informed severity assessments.
Schedule: Daily at 11 PM. Avg runtime: 3-5 minutes.
Pattern 2: Docs Drift Detector
Weekly scan of all merged PRs. For each PR, the routine identifies documentation files that reference modified functions, APIs, or configuration options. If docs are outdated relative to code changes, it opens a PR with suggested updates.
Schedule: Weekly, Sunday night. Branch: claude/docs-drift-{date}
Pattern 3: Deploy Verification
API-triggered via /fire endpoint from the CI pipeline post-deploy. The routine runs smoke tests against staging, checks for runtime errors in the last 10 minutes of logs, and either confirms deployment health or alerts with specific failure details.
Trigger: API (called by GitHub Actions after deploy step).
Pattern 4: Competitor API Monitor
Daily check of competitor changelog pages and API documentation. The routine diffs against the previous day's snapshot, summarizes changes, and flags anything that affects our integration or competitive position.
Schedule: Daily at 7 AM. Output: Slack channel + saved snapshot.
Pattern 5: Weekly Architecture Report
Scans the codebase for tech debt patterns: TODO comments older than 30 days, unused exports, circular dependencies, and test coverage gaps. Generates a prioritized cleanup list ranked by blast radius.
Schedule: Weekly, Friday at 4 PM. Branch: claude/arch-report-{date}
The Trade-Off Matrix
| Dimension | Claude Routines | n8n | Custom Cron |
|---|---|---|---|
| Setup complexity | Low (natural language) | Medium (visual builder) | High (scripts) |
| Error recovery | Self-healing (reasoning) | Manual retry config | Manual debugging |
| Integration count | MCP ecosystem (growing) | 400+ native | Unlimited (code) |
| Observability | Run logs | Full execution trace | Custom logging |
| Rate limits | 5-25 runs/day | Unlimited (self-hosted) | Unlimited |
| Idempotency | None (no dedup key) | Built-in | Custom |
| Cost | $20-100/mo (plan) | Free (self-hosted) | Server cost |
| Self-hosting | No (cloud only) | Yes | Yes |
When routines win: Reasoning-heavy tasks with variable input. Classification, drafting, code analysis, adaptive error handling.
When n8n wins: Pure data plumbing. High-volume webhook chains. Structured ETL. Anything needing 400+ pre-built integrations or self-hosting.
The practical answer for 2026: Both. n8n handles deterministic orchestration. Routines handle tasks that require judgment.
Rate Limit Math
This is the part most guides skip.
Routine runs share the same subscription pool as interactive sessions. Pro plan: 5 runs total per day. If you run 3 routines and code interactively twice, you're done for the day.
Max plan at 15 runs/day gives breathing room, but heavy agentic tasks can burn through faster than expected. Multiple Max users have reported 90-minute burnout on intensive sessions.
Capacity planning: Count your routine triggers per day. Add your expected interactive sessions. Stay under 70% of your daily limit to avoid hitting walls during critical coding sessions.
Research Preview: What Will Break
The /fire endpoint requires the anthropic-beta: experimental-cc-routine-2026-04-01 header. "Experimental" means the API surface WILL change. Anthropic guarantees the two most recent header versions continue working, giving you migration time — but don't build business-critical infrastructure on the assumption that today's endpoint shape is permanent.
Key Takeaways
- Routines run full Claude Code sessions with reasoning — not simple script execution
- Three trigger types (schedule, API, GitHub) are combinable on a single routine
- No idempotency key on /fire — build a dedup layer for webhook architectures
- Rate limits are shared with interactive sessions — capacity plan accordingly
- n8n still wins for data plumbing; routines win for reasoning-heavy tasks
The Full Implementation
The production playbook with complete code for all 5 patterns — including the /fire API integration, MCP connector configs, the dedup layer, and the monitoring setup — is in the resource below.